Prepared by:
HALBORN
Last Updated 12/02/2024
Date of Engagement: November 22nd, 2024 - November 26th, 2024
Summary
100% of all REPORTED Findings have been addressed
All findings
3
Critical
0
High
0
Medium
0
Low
2
Informational
1
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Unsafe downcasting of rewards in restake function
- 7.2 Token dust accumulation in dynexholderincentiveprogram
- 7.3 Missing reward duration check
- 8. Automated Testing
1. Introduction
Dynex engaged Halborn to conduct a security assessment on their smart contracts beginning on November 22nd, 2024 and ending on November 26th, 2024. The security assessment was scoped to the smart contracts provided to the Halborn team.
2. Assessment Summary
The team at Halborn was provided 3 days for the engagement and assigned a security engineer to evaluate the security of the smart contract.
The security engineer is a blockchain and smart-contract security expert with advanced penetration testing, smart-contract hacking, and deep knowledge of multiple blockchain protocols.
The purpose of this assessment is to:
Ensure that smart contract functions operate as intended.
Identify potential security issues with the smart contracts.
In summary, Halborn identified some improvements to reduce the likelihood and impact of risks, which were partially addressed by the Dynex team:
Downcast variables in a safe way.Prevent dust from being accumulated in the contract.Add security checks.
3. Test Approach and Methodology
Halborn performed a combination of manual and automated security testing to balance efficiency, timeliness, practicality, and accuracy regarding the scope of this assessment. While manual testing is recommended to uncover flaws in logic, process, and implementation; automated testing techniques help enhance code coverage and quickly identify items that do not follow the security best practices. The following phases and associated tools were used during the assessment:
Research into architecture and purpose.
Smart contract manual code review and walkthrough.
Graphing out functionality and contract logic/connectivity/functions. (
solgraph,draw.io)Manual assessment of use and safety for the critical Solidity variables and functions in scope to identify any arithmetic related vulnerability classes.
Manual testing by custom scripts.
Static Analysis of security for scoped contract, and imported functions. (
Slither)Testnet deployment. (
Hardhat,Foundry)
4. RISK METHODOLOGY
4.1 EXPLOITABILITY
Attack Origin (AO):
Attack Cost (AC):
Attack Complexity (AX):
Metrics:
| EXPLOITABILITY METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Attack Origin (AO) | Arbitrary (AO:A) Specific (AO:S) | 1 0.2 |
| Attack Cost (AC) | Low (AC:L) Medium (AC:M) High (AC:H) | 1 0.67 0.33 |
| Attack Complexity (AX) | Low (AX:L) Medium (AX:M) High (AX:H) | 1 0.67 0.33 |
4.2 IMPACT
Confidentiality (C):
Integrity (I):
Availability (A):
Deposit (D):
Yield (Y):
Metrics:
| IMPACT METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Confidentiality (C) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Integrity (I) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Availability (A) | None (A:N) Low (A:L) Medium (A:M) High (A:H) Critical (A:C) | 0 0.25 0.5 0.75 1 |
| Deposit (D) | None (D:N) Low (D:L) Medium (D:M) High (D:H) Critical (D:C) | 0 0.25 0.5 0.75 1 |
| Yield (Y) | None (Y:N) Low (Y:L) Medium (Y:M) High (Y:H) Critical (Y:C) | 0 0.25 0.5 0.75 1 |
4.3 SEVERITY COEFFICIENT
Reversibility (R):
Scope (S):
Metrics:
| SEVERITY COEFFICIENT () | COEFFICIENT VALUE | NUMERICAL VALUE |
|---|---|---|
| Reversibility () | None (R:N) Partial (R:P) Full (R:F) | 1 0.5 0.25 |
| Scope () | Changed (S:C) Unchanged (S:U) | 1.25 1 |
| Severity | Score Value Range |
|---|---|
| Critical | 9 - 10 |
| High | 7 - 8.9 |
| Medium | 4.5 - 6.9 |
| Low | 2 - 4.4 |
| Informational | 0 - 1.9 |
5. SCOPE
- IDynexHolderIncentiveProgram
- DynexHolderIncentiveProgram
6. Assessment Summary & Findings Overview
Critical
0
High
0
Medium
0
Low
2
Informational
1
| Security analysis | Risk level | Remediation Date |
|---|---|---|
| Unsafe Downcasting of Rewards in restake Function | Low | Not Applicable - 11/29/2024 |
| Token Dust Accumulation in DynexHolderIncentiveProgram | Low | Risk Accepted |
| Missing Reward Duration Check | Informational | Solved - 11/28/2024 |
7. Findings & Tech Details
7.1 Unsafe Downcasting of Rewards in restake Function
//
Description
The DynexHolderIncentiveProgram contract performs unsafe downcasting from uint128 to uint64 in the restake() and exit() functions when handling user rewards. This causes silent truncation of reward values that exceed the maximum value of uint64 (e.g.: 2^64 - 1):
function restake() public whenNotPaused updateReward(msg.sender) {
uint64 reward = uint64(usersInfo[msg.sender].reward);
// ... // function exit() external
{
withdraw(uint64(usersInfo[msg.sender].balance));
getReward();
} The contract stores user rewards as uint128 in the UserInfo struct:
struct UserInfo {
uint256 rewardPerTokenPaid;
uint128 reward;//E total rewards earned by the user.
uint128 balance;When accumulated rewards exceed 2^64 - 1 (18.446 quintillion), the following security issues occur:
The
restake()function silently truncates rewards above uint64 max, resulting in permanent loss of user rewardsThe
exit()function fails to withdraw the full balance due to the same truncation issueUsers with large accumulated rewards become unable to use these core contract functions
Proof of Concept
This test can be added to stake.test.ts :
describe("unsafe casting vulnerabilities", () => {
let defaultAdmin: HardhatEthersSigner,
rewardsDistribution: HardhatEthersSigner,
user: HardhatEthersSigner,
DHIPcontract: DynexHolderIncentiveProgram,
dnxToken: ERC20Mock,
userAddress: Address;
const UINT64_MAX = BigInt(2 ** 64) - 1n;
const stakeAmount = ethers.parseUnits("100000", DNX_DECIMALS);
it("Should deploy and initialize contract", async () => {
const deployStakingFixture = () => deployStaking(DNX_DECIMALS, ONE_MONTH);
const deployment = await loadFixture(deployStakingFixture);
defaultAdmin = deployment.defaultAdmin;
rewardsDistribution = deployment.rewardsDistribution;
user = deployment.user;
DHIPcontract = deployment.DHIPcontract;
dnxToken = deployment.dnxToken;
userAddress = await user.getAddress();
});
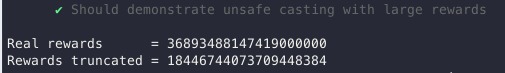
it("Should demonstrate unsafe casting with large rewards", async () => {
// First stake a normal amount
await dnxToken.connect(user).approve(await DHIPcontract.getAddress(), stakeAmount);
await DHIPcontract.connect(user).stake(stakeAmount);
// Set up a reward scenario that will lead to large accumulation
const massiveReward = UINT64_MAX; // Just under the uint64 max
await dnxToken.connect(defaultAdmin).transfer(await DHIPcontract.getAddress(), massiveReward);
// Set a very short duration to force high reward rate
await DHIPcontract.connect(defaultAdmin).setRewardsDuration(1); // 1 second duration
await DHIPcontract.connect(rewardsDistribution).notifyRewardAmount(massiveReward);
// Wait to accumulate rewards
await skipTime(2);
await dnxToken.connect(defaultAdmin).transfer(await DHIPcontract.getAddress(), massiveReward);
await DHIPcontract.connect(rewardsDistribution).notifyRewardAmount(massiveReward);
await skipTime(2);
const UINT64_MAX2 = BigInt(2 ** 65) - 2n;
console.log("Rewards for user should be = %s",UINT64_MAX2);
// Try to restake - should fail due to unsafe casting
DHIPcontract.connect(user).restake();
// Try to exit - should also fail
DHIPcontract.connect(user).exit();
});
}); And the result is :
BVSS
Recommendation
It is recommended to replace the unsafe casting with safe operations or to not cast at all:
function restake() public whenNotPaused updateReward(msg.sender) {
uint128 reward = usersInfo[msg.sender].reward;
if (reward > type(uint64).max) revert RewardTooLarge();
if (reward > 0) {
usersInfo[msg.sender].reward = 0;
totalSupply += uint64(reward);
usersInfo[msg.sender].balance += uint64(reward);
emit Restake(msg.sender, uint64(reward));
}
else {
revert ZeroAmount();
}
}Similarly for the exit() function:
function exit() external {
uint128 balance = usersInfo[msg.sender].balance;
if (balance > type(uint64).max) revert BalanceTooLarge();
withdraw(uint64(balance));
getReward();
}Add appropriate error definitions:
error RewardTooLarge();
error BalanceTooLarge();Remediation
NOT APPLICABLE: This contract will be used exactly for 0xDNX token which has 9 decimals and HARD_CAP=110000000000000000. Therefore, the maximum value of tokens can be stored in uint64, and the reward less than HARD_CAP, so this is not an issue.
References
7.2 Token Dust Accumulation in DynexHolderIncentiveProgram
//
Description
The DynexHolderIncentiveProgram contract accumulates dust amounts of tokens due to integer division rounding in reward calculations. This occurs in multiple locations:
rewardRate = reward / rewardsDuration;
return rewardPerTokenStored + (((lastTimeRewardApplicable() - lastUpdateTime) * rewardRate * 10 ** decimals) / totalSupply);In a test scenario with:
Initial reward amount: 1,000,000 DNX
Two users staking equal amounts
Full reward period completion
Both users exiting completely
The contract retains 0.001158 DNX (1,158,000,000 wei) that is inaccessible to users. This is demonstrated by the following test outputs:
Alice Earned Total: 499,999,228,100,000
Bob Earned Total: 499,999,613,900,000
Remaining in Contract: 1,158,000,000The total distributed amount is less than the initial reward amount due to these rounding errors.
The issue compounds with each reward period
Over multiple reward cycles with large amounts, the locked tokens represent a direct loss of value for the protocol
No existing mechanism to recover these locked tokens
For example, with weekly reward distributions of 1M DNX over a year, this results in approximately 0.06 DNX locked per period, accumulating to 3.12 DNX annually, this amount is very low but still exists.
BVSS
Recommendation
It is recommended to add a recovery mechanism for dust amounts:
function recoverDust() external onlyRole(DEFAULT_ADMIN_ROLE) {
uint256 currentBalance = dnxToken.balanceOf(address(this));
uint256 stakedBalance = totalSupply;
require(block.timestamp > periodFinish, "Active reward period");
require(currentBalance > stakedBalance, "No dust to recover");
uint256 dustAmount = currentBalance - stakedBalance;
dnxToken.safeTransfer(msg.sender, dustAmount);
emit DustRecovered(msg.sender, dustAmount);
}Remediation
RISK ACCEPTED: The Dynex team considered this risk as acceptable and will not implement a solution.
References
7.3 Missing Reward Duration Check
//
Description
The notifyRewardAmount function performs integer division that truncates to zero when the reward amount is less than the reward duration. This leads to a complete loss of rewards.
function notifyRewardAmount(uint64 reward) external onlyRole(REWARDS_DISTRIBUTION_ROLE) updateReward(address(0)) {
if (block.timestamp >= periodFinish) {
rewardRate = reward / rewardsDuration;When reward < rewardsDuration, the division reward / rewardsDuration truncates to 0. This behavior is demonstrated with:
reward = 2,591,999
rewardsDuration = 2,592,000
resulting rewardRate = 0
A rewardRate of 0 leads to no rewards being distributed to stakers despite tokens being allocated for rewards.
function rewardPerToken() public view returns (uint256) {
if (totalSupply == 0) return rewardPerTokenStored;
return
rewardPerTokenStored +
(((lastTimeRewardApplicable() - lastUpdateTime) * rewardRate * 10 ** decimals) / totalSupply);
}With rewardRate = 0, rewardPerToken() will not increase, resulting in no rewards' accumulation.
BVSS
Recommendation
It is recommended to implement a minimum reward amount check:
function notifyRewardAmount(uint64 reward) external onlyRole(REWARDS_DISTRIBUTION_ROLE) updateReward(address(0)) {
if (reward < rewardsDuration) revert RewardTooLow();
if (block.timestamp >= periodFinish) {
rewardRate = reward / rewardsDuration;
}
// ... rest of the function
}Add the error:
error RewardTooLow();This ensures reward amounts will always result in a non-zero reward rate, preventing silent failures in the reward distribution mechanism.
Remediation
SOLVED: A check was added by Dynex team to ensure that reward > rewardsDuration.
Remediation Hash
References
8. Automated Testing
Halborn used automated testing techniques to enhance the coverage of certain areas of the smart contracts in scope. Among the tools used was Slither, a Solidity static analysis framework.
After Halborn verified the smart contracts in the repository and was able to compile them correctly into their abis and binary format, Slither was run against the contracts. This tool can statically verify mathematical relationships between Solidity variables to detect invalid or inconsistent usage of the contracts' APIs across the entire code-base.
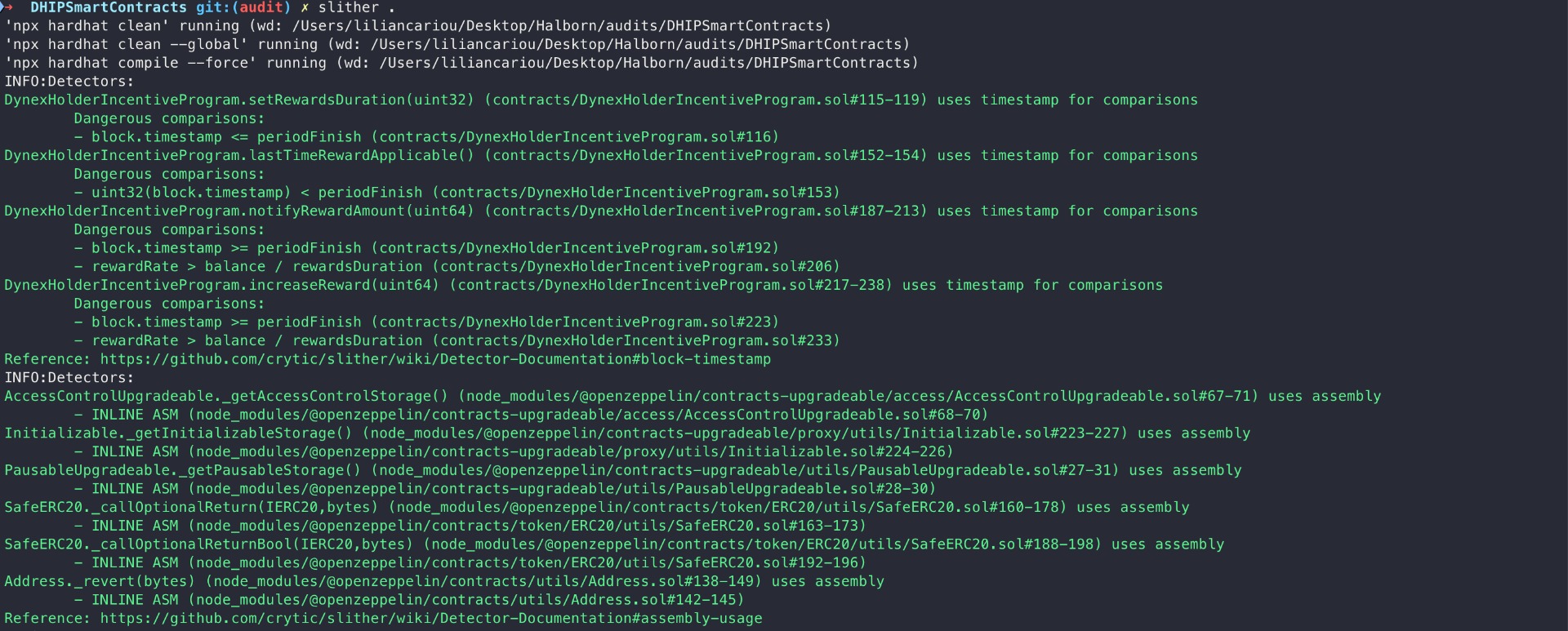
All issues identified by Slither were proved to be false positives or have been added to the issue list in this report.
Halborn strongly recommends conducting a follow-up assessment of the project either within six months or immediately following any material changes to the codebase, whichever comes first. This approach is crucial for maintaining the project’s integrity and addressing potential vulnerabilities introduced by code modifications.
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Unsafe downcasting of rewards in restake function
- 7.2 Token dust accumulation in dynexholderincentiveprogram
- 7.3 Missing reward duration check
- 8. Automated Testing
// Download the full report
* Use Google Chrome for best results
** Check "Background Graphics" in the print settings if needed
