Prepared by:
HALBORN
Last Updated 08/19/2024
Date of Engagement: July 22nd, 2024 - July 26th, 2024
Summary
100% of all REPORTED Findings have been addressed
All findings
4
Critical
0
High
0
Medium
0
Low
1
Informational
3
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Use of constant value to absorb rounding errors
- 7.2 Lack of zero address checks
- 7.3 Unused function arguments
- 7.4 Redundant check in balance and debt verification
- 8. Automated Testing
1. Introduction
Maha engaged Halborn to conduct a security assessment on their smart contracts beginning on July 22nd and ending on July 26th. The security assessment was scoped to the smart contracts provided in the GitHub repository [mahaxyz](https://github.com/mahaxyz/), commit hashes, and further details can be found in the Scope section of this report.
The scope included in this assessment includes the core of the MAHA protocol which is focused on the creation of ZAI token USDz, a stable coin with the following characteristics:
Fully pegged to USD fiat by minting 1:1 to already pegged USDC token, used as collateral, and assuring peg with a custom Peg Stability Module.
USDzis a LayerZero'sOFT, which means that it will be able to be sent (minted in)to all blockchains supported by LayerZero.ZAI can be staked in a dedicated Morpho Blue trustless lending market.
2. Assessment Summary
The team at Halborn was provided 1 week for the engagement and assigned one full-time security engineer to check the security of the smart contract. The security engineer is a blockchain and smart-contract security experts with advanced penetration testing, smart-contract hacking, and deep knowledge of multiple blockchain protocols.
The purpose of this assessment is to:
Ensure that smart contract functions operate as intended.
Identify potential security issues with the smart contracts.
3. Test Approach and Methodology
Halborn performed a combination of manual review of the code and automated security testing to balance efficiency, timeliness, practicality, and accuracy in regard to the scope of the smart contract assessment. While manual testing is recommended to uncover flaws in logic, process, and implementation; automated testing techniques help enhance coverage of smart contracts and can quickly identify items that do not follow security best practices.
The following phases and associated tools were used throughout the term of the assessment:
Research into the architecture, purpose, and use of the platform.
Smart contract manual code review and walkthrough to identify any logic issue.
Thorough assessment of safety and usage of critical Solidity variables and functions in scope that could led to arithmetic related vulnerabilities.
Manual testing by custom scripts.
Graphing out functionality and contract logic/connectivity/functions (`solgraph`).
Static Analysis of security for scoped contract, and imported functions. (`Slither`).
4. RISK METHODOLOGY
4.1 EXPLOITABILITY
Attack Origin (AO):
Attack Cost (AC):
Attack Complexity (AX):
Metrics:
| EXPLOITABILITY METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Attack Origin (AO) | Arbitrary (AO:A) Specific (AO:S) | 1 0.2 |
| Attack Cost (AC) | Low (AC:L) Medium (AC:M) High (AC:H) | 1 0.67 0.33 |
| Attack Complexity (AX) | Low (AX:L) Medium (AX:M) High (AX:H) | 1 0.67 0.33 |
4.2 IMPACT
Confidentiality (C):
Integrity (I):
Availability (A):
Deposit (D):
Yield (Y):
Metrics:
| IMPACT METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Confidentiality (C) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Integrity (I) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Availability (A) | None (A:N) Low (A:L) Medium (A:M) High (A:H) Critical (A:C) | 0 0.25 0.5 0.75 1 |
| Deposit (D) | None (D:N) Low (D:L) Medium (D:M) High (D:H) Critical (D:C) | 0 0.25 0.5 0.75 1 |
| Yield (Y) | None (Y:N) Low (Y:L) Medium (Y:M) High (Y:H) Critical (Y:C) | 0 0.25 0.5 0.75 1 |
4.3 SEVERITY COEFFICIENT
Reversibility (R):
Scope (S):
Metrics:
| SEVERITY COEFFICIENT () | COEFFICIENT VALUE | NUMERICAL VALUE |
|---|---|---|
| Reversibility () | None (R:N) Partial (R:P) Full (R:F) | 1 0.5 0.25 |
| Scope () | Changed (S:C) Unchanged (S:U) | 1.25 1 |
| Severity | Score Value Range |
|---|---|
| Critical | 9 - 10 |
| High | 7 - 8.9 |
| Medium | 4.5 - 6.9 |
| Low | 2 - 4.4 |
| Informational | 0 - 1.9 |
5. SCOPE
- contracts/core/ZaiStablecoin.sol
- contracts/core/direct-deposit/Constants.sol
- contracts/core/direct-deposit/DDHub.sol
6. Assessment Summary & Findings Overview
Critical
0
High
0
Medium
0
Low
1
Informational
3
| Security analysis | Risk level | Remediation Date |
|---|---|---|
| Use of Constant Value to Absorb Rounding Errors | Low | Solved - 07/29/2024 |
| Lack of zero address checks | Informational | Acknowledged |
| Unused Function Arguments | Informational | Solved - 07/29/2024 |
| Redundant Check in Balance and Debt Verification | Informational | Acknowledged |
7. Findings & Tech Details
7.1 Use of Constant Value to Absorb Rounding Errors
//
Description
Utilizing the constant WAD (10^18) to absorb rounding errors is inappropriate for tokens like USDC, which operate with 6 decimal places (10^6). Applying WAD to USDC can lead to significant inaccuracies and out-of-range errors, as the precision mismatch can result in values that exceed the token’s operational limits.
// It's adding up `WAD` due possible rounding errors
if (!info.isLive || !info.plan.active() || currentAssets + Constants.WAD < info.debt) {
toWithdraw = maxWithdraw;
} else {
uint256 maxDebt = info.debtCeiling; //vat.Line();
uint256 debt = info.debt;
...Therefore, when working with USDC, it's being created a range to absorb rounding errors of 10^12 USDC, which is undoubtedly an exaggerated range.
BVSS
Recommendation
Creating/using a dynamic value to fit better the "rounding error" range is recommendable. This can be easily achievable by calling token.decimals() or storing this value in the pool info.
Remediation Plan
SOLVED: The Maha team removed completely this part of the conditional to focus on the contract being checked as active and live.
Remediation Hash
7.2 Lack of zero address checks
//
Description
The initialize function in the PegStabilityModule lacks validation checks for zero addresses, potentially leading to critical issues. Initializing contracts with zero addresses can result in unexpected behavior or security vulnerabilities, as zero addresses may represent invalid or unintentional destinations. Implementing checks to ensure addresses are not zero is essential to maintain contract integrity, prevent errors, and enhance overall security.
Besides, there are no zero checks in the following functions either:
mintredeemupdateFeeDestination
Regarding the contract DDHub.sol:
initializesetFeeCollector
BVSS
Recommendation
Consider including pertinent address checks.
Remediation Plan
ACKNOWLEDGED: The Maha team acknowledged this issue.
7.3 Unused Function Arguments
//
Description
In the DDOperatorPlan contract we find that getTargetAssets has a not used argument.
function getTargetAssets(uint256) external view override returns (uint256) {
if (enabled == 0) return 0;
return targetAssets;
}Besides, there's a call in contract DDHUB.sol that can be cleaned too:
uint256 targetAssets = info.plan.getTargetAssets(currentAssets);BVSS
Recommendation
Unused arguments should be cleaned up from the code if they have no purpose. Clearing these arguments will increase the readability of the code.
Remediation Plan
SOLVED: The Maha team decided to maintain this unused variable, as it will be used in future improvements of the protocol.
Remediation Hash
7.4 Redundant Check in Balance and Debt Verification
//
Description
The provided code contains a redundant check that can be streamlined for efficiency. The require statement verifies that the balance plus 1 wei is greater than or equal to the debt, followed by an if statement that returns if the balance is less than or equal to the debt. The require statement makes the subsequent if check unnecessary because if the condition in require fails, the function execution is halted.
require(balanceBefore + 1 wei >= info.debt, "invaraint balance >= debt");
// calculate fees
if (balanceBefore <= info.debt) return;BVSS
Recommendation
The require statement can be refined to remove redundancy, and the if check can be eliminated.
require(balanceBefore > info.debt, "invariant balance > debt");Remediation Plan
ACKNOWLEDGED: The Maha team acknowledged this issue.
8. Automated Testing
Description
Halborn used automated testing techniques to enhance the coverage of certain areas of the scoped contracts. Among the tools used was Slither, a Solidity static analysis framework. After Halborn verified all the contracts in the repository and was able to compile them correctly into their abi and binary formats, Slither was run on the all-scoped contracts. This tool can statically verify mathematical relationships between Solidity variables to detect invalid or inconsistent usage of the contracts' APIs across the entire code-base.
Slither results
ERC20 Specific
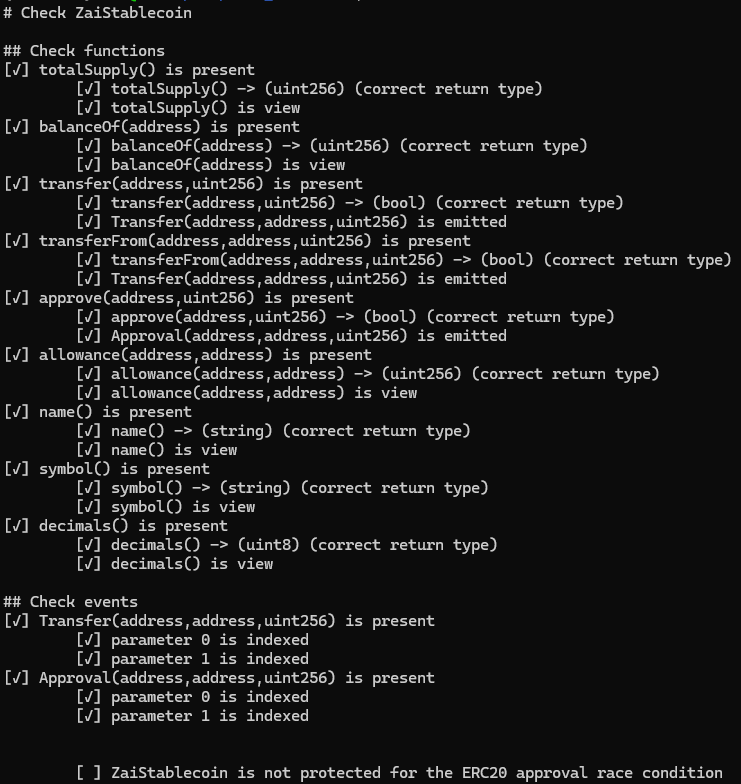
As USDz inherits ERC20permit, approvals aren't expected to be used, otherwise "ERC20 appoval race condition" should be taken into account.
Core analysis
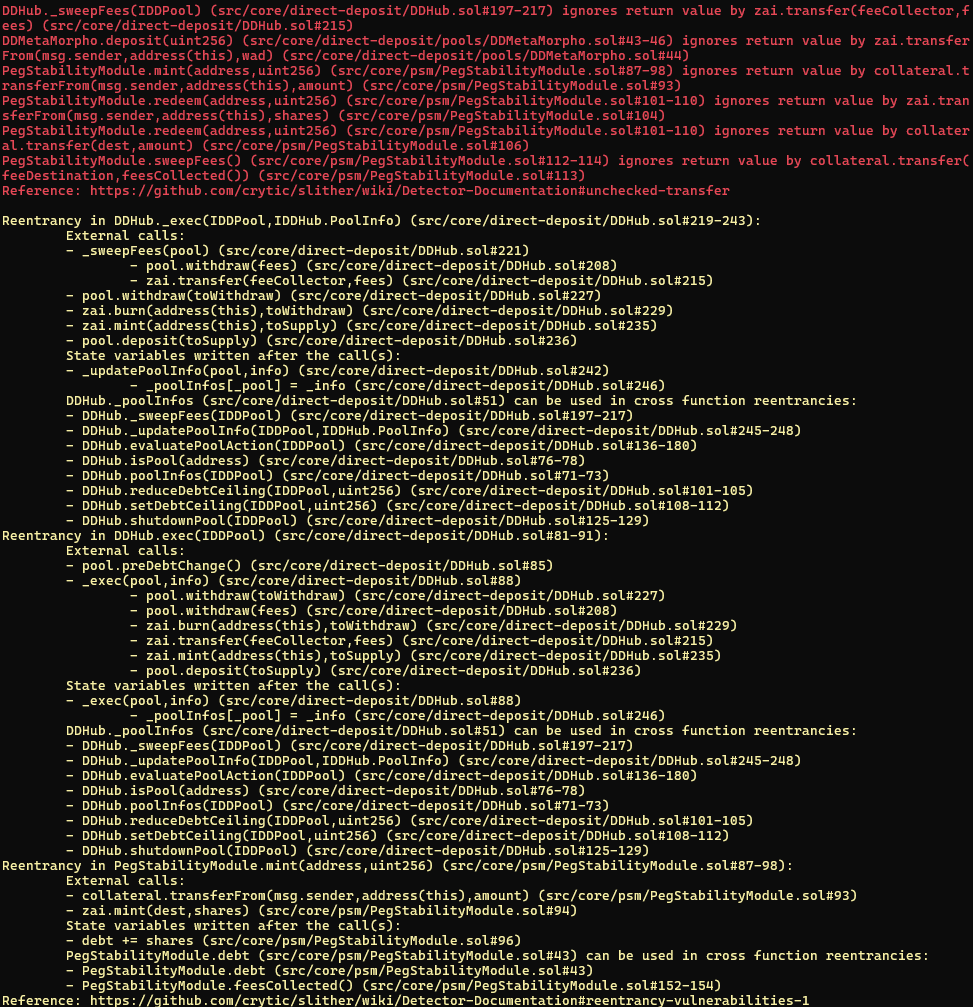
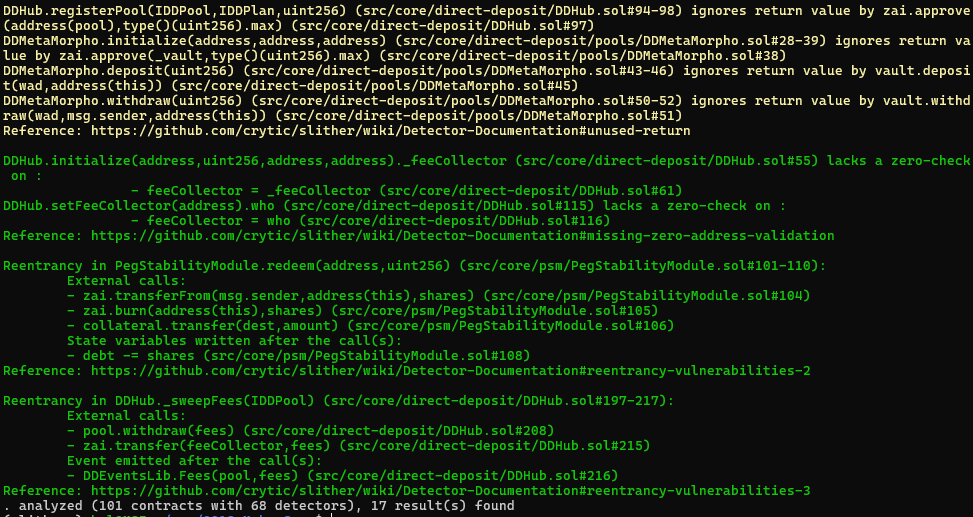
The reentrancy instances flagged by Slither were checked individually, and have been categorised as false positives. The ones that may be vulnerable are all protected with the nonReentrant modifier.
Halborn strongly recommends conducting a follow-up assessment of the project either within six months or immediately following any material changes to the codebase, whichever comes first. This approach is crucial for maintaining the project’s integrity and addressing potential vulnerabilities introduced by code modifications.
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Use of constant value to absorb rounding errors
- 7.2 Lack of zero address checks
- 7.3 Unused function arguments
- 7.4 Redundant check in balance and debt verification
- 8. Automated Testing
// Download the full report
* Use Google Chrome for best results
** Check "Background Graphics" in the print settings if needed
