Prepared by:
HALBORN
Last Updated 04/23/2024
Date of Engagement: April 8th, 2024 - April 10th, 2024
Summary
No Reported Findings to Address
All findings
0
Critical
0
High
0
Medium
0
Low
0
Informational
0
Table of Contents
1. Introduction
Moonwell engaged Halborn to conduct a security assessment on their AxelarBridgeAdapter.sol smart contract beginning on April 8th and ending on April 10th. The security assessment was scoped to the smart contract provided in the moonwell-fi/moonwell-contracts-v2 GitHub repository. Commit hash and further details can be found in the Scope section of this report.
2. Assessment Summary
Halborn was provided 2 days for the engagement and assigned 1 full-time security engineer to review the security of the smart contract in scope. The engineer is a blockchain and smart contract security expert with advanced penetration testing and smart contract hacking skills, and deep knowledge of multiple blockchain protocols.
The purpose of the assessment is to:
Identify potential security issues within the smart contract
AxelarBridgeAdapter.sol.Ensure that smart contract functionality operates as intended.
In summary, Halborn has not identified any security risk inherent to the contract under analysis, given the engagement scope.
3. Test Approach and Methodology
Halborn performed a combination of manual and automated security testing to balance efficiency, timeliness, practicality, and accuracy in regard to the scope of this assessment. While manual testing is recommended to uncover flaws in logic, process, and implementation; automated testing techniques help enhance coverage of the code and can quickly identify items that do not follow the security best practices. The following phases and associated tools were used during the assessment:
Research into architecture and purpose.
Smart contract manual code review and walkthrough.
Graphing out functionality and contract logic/connectivity/functions (
solgraph).Manual assessment of use and safety for the critical Solidity variables and functions in scope to identify any arithmetic-related vulnerability classes.
Manual testing by custom scripts.
Static Analysis of security for scoped contract, and imported functions (
slither).Testnet deployment (
Foundry).
4. Manual Testing
The contract in scope was thoroughly and manually analyzed for potential vulnerabilities and bugs, as well as known optimizations and best practices when developing Smart Contracts in Solidity.
While no major vulnerabilities were found within the scope and time frame provided, it's always important to highlight good practices that were identified during the assessment, which contribute positively to the security maturity of the contracts in-scope, such as:
- Thorough documentation using NatSpec.
- The use of unchecked blocks in for loops extends gas optimization.
- The usage of Ownable2Step pattern is considered a good security practice and mitigates this risk by introducing a two-step process for ownership transfer. The current owner initiates the transfer by proposing a new owner, but the transfer only completes when the proposed new owner accepts it.
- Contract calls are validated in the execute function through the call to gateway.validateContractCall, this helps preventing unallowed actions passing through the execution mechanism.
These security practices are applied industry-wide and should be preserved in future implementations and developments.
5. RISK METHODOLOGY
5.1 EXPLOITABILITY
Attack Origin (AO):
Attack Cost (AC):
Attack Complexity (AX):
Metrics:
| EXPLOITABILITY METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Attack Origin (AO) | Arbitrary (AO:A) Specific (AO:S) | 1 0.2 |
| Attack Cost (AC) | Low (AC:L) Medium (AC:M) High (AC:H) | 1 0.67 0.33 |
| Attack Complexity (AX) | Low (AX:L) Medium (AX:M) High (AX:H) | 1 0.67 0.33 |
5.2 IMPACT
Confidentiality (C):
Integrity (I):
Availability (A):
Deposit (D):
Yield (Y):
Metrics:
| IMPACT METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Confidentiality (C) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Integrity (I) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Availability (A) | None (A:N) Low (A:L) Medium (A:M) High (A:H) Critical (A:C) | 0 0.25 0.5 0.75 1 |
| Deposit (D) | None (D:N) Low (D:L) Medium (D:M) High (D:H) Critical (D:C) | 0 0.25 0.5 0.75 1 |
| Yield (Y) | None (Y:N) Low (Y:L) Medium (Y:M) High (Y:H) Critical (Y:C) | 0 0.25 0.5 0.75 1 |
5.3 SEVERITY COEFFICIENT
Reversibility (R):
Scope (S):
Metrics:
| SEVERITY COEFFICIENT () | COEFFICIENT VALUE | NUMERICAL VALUE |
|---|---|---|
| Reversibility () | None (R:N) Partial (R:P) Full (R:F) | 1 0.5 0.25 |
| Scope () | Changed (S:C) Unchanged (S:U) | 1.25 1 |
| Severity | Score Value Range |
|---|---|
| Critical | 9 - 10 |
| High | 7 - 8.9 |
| Medium | 4.5 - 6.9 |
| Low | 2 - 4.4 |
| Informational | 0 - 1.9 |
6. SCOPE
- src/xWELL/AxelarBridgeAdapter.sol
7. Assessment Summary & Findings Overview
Critical
0
High
0
Medium
0
Low
0
Informational
0
| Security analysis | Risk level | Remediation Date |
|---|
8. Findings & Tech Details
9. Review Notes
Removed style/optimization issues from final report as requested by client.
10. Automated Testing
Introduction
Halborn used automated testing techniques to enhance the coverage of certain areas of the smart contract in scope. Among the tools used was Slither, a Solidity static analysis framework. After Halborn verified the smart contract in the repository and was able to compile it correctly into their ABI and binary format, Slither was run against the contract. This tool can statically verify mathematical relationships between Solidity variables to detect invalid or inconsistent usage of the contract's API across the entire code-base.
The security team assessed all findings identified by the Slither software, and findings with severity Information and Optimization are also included in the below results.
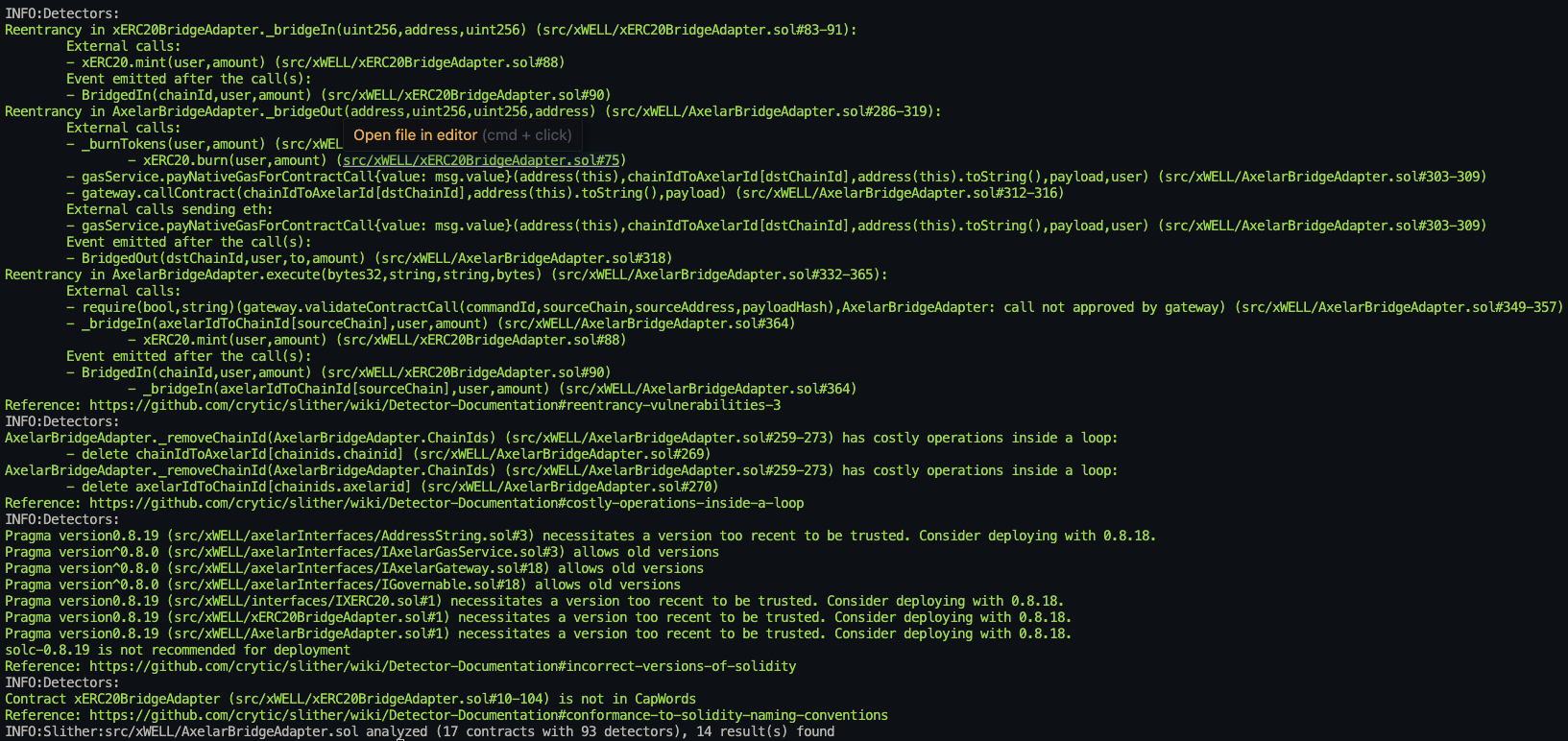
The findings obtained as a result of the Slither scan were reviewed, and they were not included in the report because they were determined false positives.
Halborn strongly recommends conducting a follow-up assessment of the project either within six months or immediately following any material changes to the codebase, whichever comes first. This approach is crucial for maintaining the project’s integrity and addressing potential vulnerabilities introduced by code modifications.
Table of Contents
// Download the full report
* Use Google Chrome for best results
** Check "Background Graphics" in the print settings if needed
