Prepared by:
HALBORN
Last Updated 08/05/2024
Date of Engagement: June 24th, 2024 - June 27th, 2024
Summary
100% of all REPORTED Findings have been addressed
All findings
8
Critical
0
High
0
Medium
0
Low
1
Informational
7
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Missing fee amounts verification
- 7.2 Non-reentrant modifier ordering
- 7.3 Open to-do
- 7.4 Incompatibility risk for evm versions in different chains
- 7.5 Floating pragma
- 7.6 Unused import
- 7.7 Dispensable gas fess from public functions not called within contract
- 7.8 Dispensable gas fees from unoptimized loops
- 8. Automated Testing
1. Introduction
The Tagus Labs team engaged Halborn to conduct a security assessment on their smart contracts beginning on 06-24-2024 and ending on 06-27-2024. The security assessment was scoped to the smart contracts provided in the https://github.com/inceptionlrt/smart-contracts GitHub repository. Commit hashes and further details can be found in the Scope section of this report. The Inceptionlrt/Smart Contracts codebase in scope mainly consists of native and isolated liquid restaking for the Eigenlayer ecosystem.
2. Assessment Summary
Halborn was provided 4 days for the engagement and assigned 1 full-time security engineer to review the security of the smart contracts in scope. The engineer is a blockchain and smart contract security expert with advanced penetration testing and smart contract hacking skills, and deep knowledge of multiple blockchain protocols.
The purpose of the assessment is to:
Identify potential security issues within the smart contracts.
Ensure that smart contract functionality operates as intended.
In summary, Halborn identified some improvements to reduce the likelihood and impact of risks, which were mostly addressed by the Tagus Labs team. The main identified issue was:
Missing fee amounts verification.
3. Test Approach and Methodology
Halborn performed a combination of manual review of the code and automated security testing to balance efficiency, timeliness, practicality, and accuracy in regard to the scope of this assessment. While manual testing is recommended to uncover flaws in logic, process, and implementation; automated testing techniques help enhance coverage of smart contracts and can quickly identify items that do not follow security best practices.
The following phases and associated tools were used throughout the term of the assessment:
Research into architecture, purpose and use of the platform.
Smart contract manual code review and walkthrough to identify any logic issue.
Thorough assessment of safety and usage of critical Solidity variables and functions in scope that could led to arithmetic related vulnerabilities.
Local testing with custom scripts (
Foundry).Fork testing against main networks (
Foundry).Static analysis of security for scoped contract, and imported functions (
Slither).
3.1 Out-of-scope
External libraries and financial-related attacks.
New features/implementations after/within the remediation commit IDs.
Changes that occur outside of the scope of PRs.
The following contracts, while they affect the in-scope code, were not specifically reviewed as part of the scope and are assumed to not contain any issues:
EigenLayerHandler.sol
InceptionAssetsHandler.sol
RatioFeed.sol
InceptionToken.sol
DelegationManager.sol
4. RISK METHODOLOGY
4.1 EXPLOITABILITY
Attack Origin (AO):
Attack Cost (AC):
Attack Complexity (AX):
Metrics:
| EXPLOITABILITY METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Attack Origin (AO) | Arbitrary (AO:A) Specific (AO:S) | 1 0.2 |
| Attack Cost (AC) | Low (AC:L) Medium (AC:M) High (AC:H) | 1 0.67 0.33 |
| Attack Complexity (AX) | Low (AX:L) Medium (AX:M) High (AX:H) | 1 0.67 0.33 |
4.2 IMPACT
Confidentiality (C):
Integrity (I):
Availability (A):
Deposit (D):
Yield (Y):
Metrics:
| IMPACT METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Confidentiality (C) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Integrity (I) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Availability (A) | None (A:N) Low (A:L) Medium (A:M) High (A:H) Critical (A:C) | 0 0.25 0.5 0.75 1 |
| Deposit (D) | None (D:N) Low (D:L) Medium (D:M) High (D:H) Critical (D:C) | 0 0.25 0.5 0.75 1 |
| Yield (Y) | None (Y:N) Low (Y:L) Medium (Y:M) High (Y:H) Critical (Y:C) | 0 0.25 0.5 0.75 1 |
4.3 SEVERITY COEFFICIENT
Reversibility (R):
Scope (S):
Metrics:
| SEVERITY COEFFICIENT () | COEFFICIENT VALUE | NUMERICAL VALUE |
|---|---|---|
| Reversibility () | None (R:N) Partial (R:P) Full (R:F) | 1 0.5 0.25 |
| Scope () | Changed (S:C) Unchanged (S:U) | 1.25 1 |
| Severity | Score Value Range |
|---|---|
| Critical | 9 - 10 |
| High | 7 - 8.9 |
| Medium | 4.5 - 6.9 |
| Low | 2 - 4.4 |
| Informational | 0 - 1.9 |
5. SCOPE
- Flash withdrawal functionality from contracts/Inception/lib/InceptionLibrary.sol
- contracts/Inception/vaults/InceptionVault.sol
6. Assessment Summary & Findings Overview
Critical
0
High
0
Medium
0
Low
1
Informational
7
| Security analysis | Risk level | Remediation Date |
|---|---|---|
| Missing fee amounts verification | Low | Solved - 06/27/2024 |
| Non-reentrant modifier ordering | Informational | Acknowledged |
| Open TO-DO | Informational | Solved - 06/27/2024 |
| Incompatibility risk for EVM versions in different chains | Informational | Acknowledged |
| Floating pragma | Informational | Acknowledged |
| Unused import | Informational | Solved - 06/27/2024 |
| Dispensable gas fess from public functions not called within contract | Informational | Solved - 06/27/2024 |
| Dispensable gas fees from unoptimized loops | Informational | Acknowledged |
7. Findings & Tech Details
7.1 Missing fee amounts verification
//
Description
In the flashWithdraw() function from the InceptionVault contract, the fee and protocolWithdrawalFee variables are not verified to be greater than zero. Although with the current implementation, it is highly unlikely to have a fee value of zero (for example, in cases where the targetCapacity value is set to a very low value), this oversight could allow a user the execution of flash withdrawals without paying the expected fee.
BVSS
Recommendation
It is recommended to add a check to ensure that the fee and protocolWithdrawalFee variables are greater than zero before proceeding with the flash withdrawal.
Remediation Plan
SOLVED: The Tagus Labs team has addressed the finding in commit 0229f48e38eacf23baa53c33190c968c8d2e324f by following the mentioned recommendation.
Remediation Hash
References
7.2 Non-reentrant modifier ordering
//
Description
In Solidity, if a function has multiple modifiers they are executed in the order specified. If checks or logic of modifiers depend on other modifiers this has to be considered in their ordering.
The flashWithdraw(), redeem() and withdraw() functions from the InceptionVault contract have multiple modifiers with one of them being nonreentrant which prevents reentrancy on the functions. This should ideally be the first one to prevent even the execution of other modifiers in case of reentrancies.
While there is currently no obvious vulnerability with nonreentrant being the last modifier in the list, placing it first ensures that all other modifiers are executed only if the call is non-reentrant. This is a safer practice and can prevent potential issues in future updates or unforeseen scenarios.
BVSS
Recommendation
Switch modifier order to consistently place the nonReentrant modifier as the first one to run so that all other modifiers are executed only if the call is non-reentrant.
Remediation Plan
ACKNOWLEDGED: The Tagus Labs team made a business decision to acknowledge this finding and not alter the contracts.
References
7.3 Open TO-DO
//
Description
The __InceptionVault_init() function from the InceptionVault contract contains a TODO comment that may indicates that the function has not been not completely implemented. This incomplete implementation can lead to unexpected behavior and/or potential vulnerabilities within the contract.
minAmount = 100;
/// @notice TODO
protocolFee = 50 * 1e8;BVSS
Recommendation
Ensure that all TODO comments are resolved and the function is fully implemented.
Remediation Plan
SOLVED: The Tagus Labs team has addressed the finding in commit 0229f48e38eacf23baa53c33190c968c8d2e324f by following the mentioned recommendation.
Remediation Hash
References
7.4 Incompatibility risk for EVM versions in different chains
//
Description
From Solidity versions 0.8.20 through 0.8.24, the default target EVM version is set to Shanghai, which results in the generation of bytecode that includes PUSH0 opcodes. Starting with version 0.8.25, the default EVM version shifts to Cancun, introducing new opcodes for transient storage, TSTORE and TLOAD.
In this aspect, it is crucial to select the appropriate EVM version when it's intended to deploy the contracts on networks other than the Ethereum mainnet, which may not support these opcodes. Failure to do so could lead to unsuccessful contract deployments or transaction execution issues.
BVSS
Recommendation
Make sure to specify the target EVM version when using Solidity versions from 0.8.20 and above if deploying to chains that may not support newly introduced opcodes. Additionally, it is crucial to stay informed about the opcode support of different chains to ensure smooth deployment and compatibility.
Remediation Plan
ACKNOWLEDGED: The Tagus Labs team made a business decision to acknowledge this finding and not alter the contracts.
7.5 Floating pragma
//
Description
The files in scope currently use floating pragma version ^0.8.22, which means that the code can be compiled by any compiler version that is greater than or equal to 0.8.22, and less than 0.9.0.
However, it is recommended that contracts should be deployed with the same compiler version and flags used during development and testing. Locking the pragma helps to ensure that contracts do not accidentally get deployed using another pragma. For example, an outdated pragma version might introduce bugs that affect the contract system negatively.
BVSS
Recommendation
Lock the pragma version to the same version used during development and testing.
Remediation Plan
ACKNOWLEDGED: The Tagus Labs team made a business decision to acknowledge this finding and not alter the contracts.
References
7.6 Unused import
//
Description
The InceptionVault contract imports the IRebalanceStrategy interface but does not use it in the contract. This can be considered as unnecessary code and should be removed to keep the code clean and easy to read.
BVSS
Recommendation
Remove the unused IRebalanceStrategy import statement.
Remediation Plan
SOLVED: The Tagus Labs team has addressed the finding in commit 0229f48e38eacf23baa53c33190c968c8d2e324f by following the mentioned recommendation.
Remediation Hash
References
7.7 Dispensable gas fess from public functions not called within contract
//
Description
Several functions throughout the files in scope currently define several functions with the public visibility modifier, even though the functions are not called from within the contract, possibly resulting in higher gas costs than necessary.
In the case of Solidity public functions, arguments of the functions are copied to memory. While on the other hand, functions with external visibility can directly read arguments from calldata. Since calldata is cheaper to access than memory, external functions result in a lower execution cost than public functions.
The affected functions are:
deposit()depositWithReferral()redeem()getTotalDeposited()getDelegatedTo()getPendingWithdrawalOf()maxDeposit()maxRedeem()
BVSS
Recommendation
Modify the aforementioned functions with the external visibility modifier.
Remediation Plan
SOLVED: The Tagus Labs team has addressed the finding in commit 0229f48e38eacf23baa53c33190c968c8d2e324f by following the mentioned recommendation.
Remediation Hash
References
7.8 Dispensable gas fees from unoptimized loops
//
Description
Throughout the code in scope, there are several instances of unoptimized for loop declarations that may incur in higher gas costs than necessary. The affected functions are:
redeem()isAbleToRedeem()getTotalDelegated()_verifyDelegated()
BVSS
Recommendation
Optimize the for loop declarations to reduce gas costs. Best practices include: the non-redundant initialization of the iterator with a default value (i = 0 instead of simply i), the use of the pre-increment operator ( ++i). Additionally, when reading from storage variables, it is recommended to reduce gas costs significantly by caching the array to read locally and iterate over it to avoid reading from storage on every iteration:
Moreover, if there are several loops in the same function, the i variable can be re-used, to be able to set the value from non-zero to zero and reduce gas costs without additional variable declaration. For example:
uint256[] memory arrayInMemory = arrayInStorage;
uint256 i;
for (; i < arrayInMemory.length ;) {
// code logic
unchecked { ++i; }
}
delete i;
uint256[] memory arrayInMemory2 = arrayInStorage2;
for (; i < arrayInMemory2.length ;) {
// code logic
unchecked { ++i; }
}Remediation Plan
ACKNOWLEDGED: The Tagus Labs team made a business decision to acknowledge this finding and not alter the contracts.
References
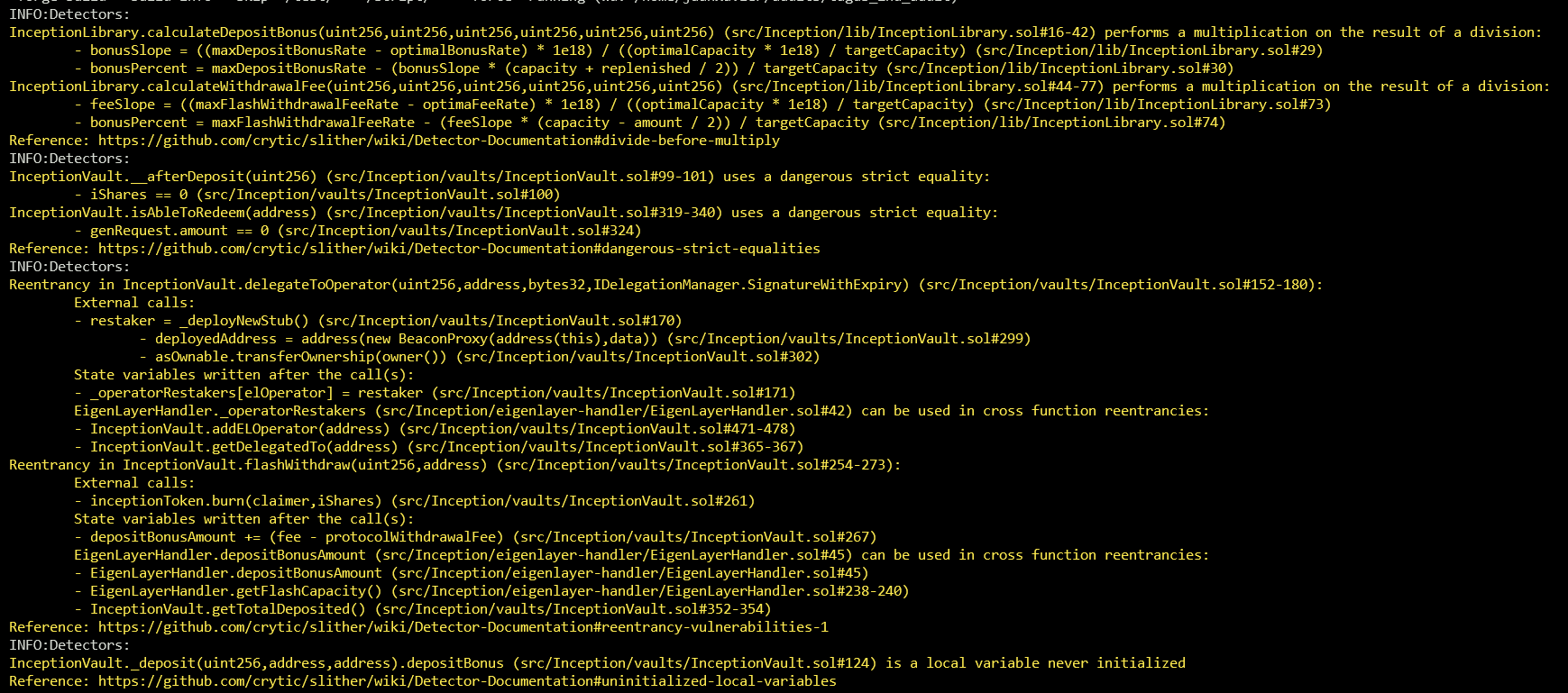
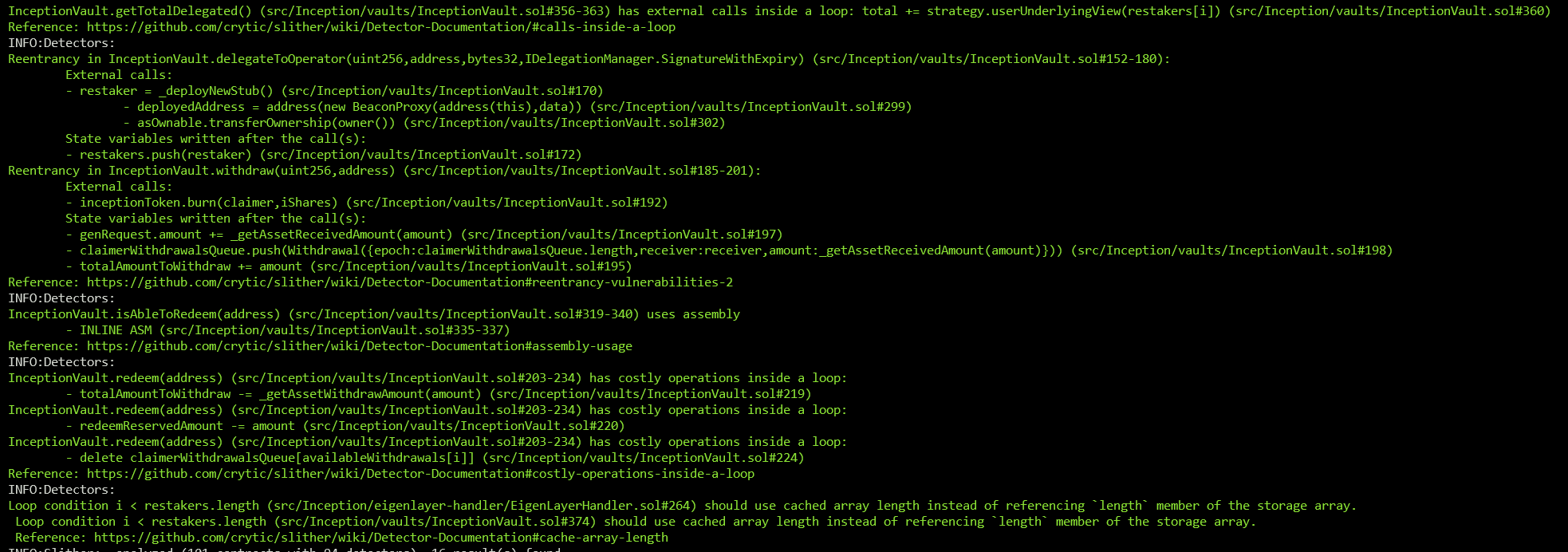
8. Automated Testing
Static Analysis Report
Description
Halborn used automated testing techniques to enhance the coverage of certain areas of the smart contracts in scope. Among the tools used was Slither, a Solidity static analysis framework. After Halborn verified the smart contracts in the repository and was able to compile them correctly into their abis and binary format, Slither was run against the contracts. This tool can statically verify mathematical relationships between Solidity variables to detect invalid or inconsistent usage of the contracts' APIs across the entire code-base.
The security team assessed all findings identified by the Slither software, however, findings with related to external dependencies are not included in the below results for the sake of report readability.
Output
The findings obtained as a result of the Slither scan were reviewed, and most of them were not included in the report because they were determined as false positives.
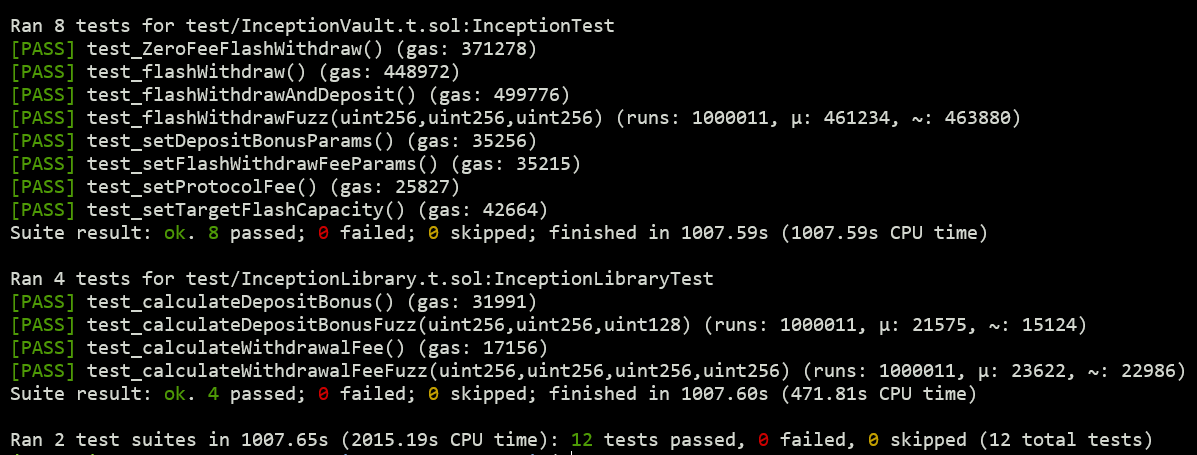
Unit tests and fuzzing
The original repository used the Hardhat environment to develop and test the smart contracts. Additionally, the project in scope was cloned to a Foundry environment, to allow for additional testing and fuzz testing that covered ~1,000,000 runs per test. These additional tests were run successfully.
Halborn strongly recommends conducting a follow-up assessment of the project either within six months or immediately following any material changes to the codebase, whichever comes first. This approach is crucial for maintaining the project’s integrity and addressing potential vulnerabilities introduced by code modifications.
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Missing fee amounts verification
- 7.2 Non-reentrant modifier ordering
- 7.3 Open to-do
- 7.4 Incompatibility risk for evm versions in different chains
- 7.5 Floating pragma
- 7.6 Unused import
- 7.7 Dispensable gas fess from public functions not called within contract
- 7.8 Dispensable gas fees from unoptimized loops
- 8. Automated Testing
// Download the full report
* Use Google Chrome for best results
** Check "Background Graphics" in the print settings if needed
